Software Updates
Updating software is one of the most effective methods of protecting computers from security vulnerabilities, yet many people and organisations choose to not install them. In this project we endevor to understand the attitudes of people making update decisions and the barriers they face that can impact their willingness and ability to keep their software up to date.
Updating software means changing it. Ideally those changes are for the better such as improved security, better features, fixed bugs, and additional functionality. However, they can also lead to worse outcomes such as slower software, new problems, changes to frequently used functionality, and new security vulnerabilities. According to our research, many of the issues around software updating are actually issues around balancing risks and benefits when neither of these are fully known. For example, the update that protected against the WannaCry ransomeware attack was made available a month before the attack happened, those that installed it were therefore protected and not impacted by the attack. But it would have been impossible for a system administrator to know at the time of update release that a devistating world wide ransomware attack was comming. Incidents like WannaCry suggest that installing patches quickly is a good idea, which is true, but it should also be understood that installing patches quickly also carries risks. For example, Microsoft released a Windows 10 update which then started deleting all the files on the desktop. They acknowledged the issue and offered a work around, but the issue was terrifying and highly disruptive for users, particularly those who installed updates quickly.
End Users
End users are regularly asked to update all types of software including: mobile apps, applications, operating systems, and firmware on devices like robot vacumes. Our work talking to end-users suggests that they do not associate updates with security, unless the software being updated has an obvious security role, such as an anti-virus. Instead they update because they feel it is something they are supposed to do. Updates are seen as necessary to get new features, fix bugs, and ensure compatability with other technologies.
End users do sometimes choose to "skip" an update or to stop updating all together. Common reasons tend to be related to risks of disruption including: unexpected user interface changes which then cost time learning new interactions, time required for the installation, potential instability of the new version, and loss of features.
System Administrators and Developers
Many serious security compromises could have been prevented using basic patch management, including WannaCry and the Experian data breach. Yet these systems are not being patched at nearly the rate security professionals would like. This project looks at system administrators and endeavor to determine the barriers they face when attempting to keep a system updated.
We studied a long-running email list dedicated to providing peer-support for system administrators who are trying to manage updates on their systems. We found that the community is an example of a Community of Practice where peer-level experts come together to solve problems jointly as well as provide education and support to others who work in a similar area. In this case, many members of the community had similar issues such as identifying
Publications
- Out of the loop: How automated software updates cause unintended security consequences [bibtex]
R. Wash, E. Rader, K. Vaniea, M. Rizor; In Symposium On Usable Privacy and Security (SOUPS). 2014. - Betrayed By Updates: How Negative Experiences Affect Future Security [bibtex]
K. Vaniea, E. Rader, R. Wash; In Proceedings of the SIGCHI Conference on Human Factors in Computing Systems. 2014. - Tales of Software Updates: The process of updating software [bibtex]
K. Vaniea, Y. Rashidi; In Proceedings of the SIGCHI Conference on Human Factors in Computing Systems. 2016. - "Anyone Else Seeing this Error?": Community, System Administrators, and Patch Information [bibtex]
A. Jenkins, P. Kalligeros, K. Vaniea, M.K. Wolters; In Proceedings of the European Symposium on Security and Privacy (EuroSP). 2020. - To Patch, or not To Patch? That is the Question: A Case Study of System Administrators' Online Collaborative Behaviour [bibtex]
A. Jenkins, M. Wolters, K. Vaniea; In arXiv. 2023.
Talks
- "Anyone Else Seeing this Error?": Community, System Administrators, and Patch Information at EuroS\&P (video)
- Tales of Software Updates: The process of updating software at SIGCHI conference (video)
- Human factors of software updates at Microsoft Research Cambridge, September 30, 2015 (video)
- Software updates: decisions and security implications talk by Kami Vaniea at the Center for Education and Research in Information Assurance and Security, Febuary 25, 2015 (video)
People
Current- Kami Vaniea
- Adam Jenkins
- Maria Wolters
- Yasmeen Rashidi
Funding
Research and projects here are partially funded by the following groups:- Google Faculty Award on Software Development of Apps
Related Student Projects
The following are projects completed by interns, undergraduate, and masters students related to the Software Update project.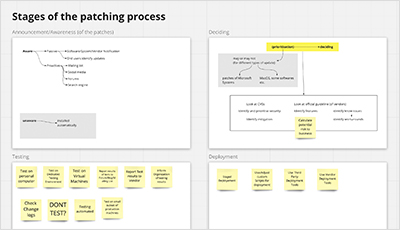
A Survey on Patching Behaviour of System Administrators
Linsen Liu
Supervisors: Kami Vaniea, Adam Jenkins
How do system administrators decide whether or not to apply a particular patch? How do they prioritise patches? How are these patches tested and deployed? There is no single best answer to these questions, as any number of factors can influence a system administrator’s patching behaviour. In this project, we designed a survey to understand the prevalence of typical patching behaviours of system administrators, and any deviations that may occur in some instances.
Why don't admins patch their systems? Analysis of an email list archive
Pieris Kalligeros
Supervisors: Kami Vaniea, Adam Jenkins
Regular application of patches (updates) is vital to the health of computer systems, but many system administrators either patch slowly or not at all. In this project, we looked at a mailing list archive where system administrators share advice about patching. The project involved building tools to automaticall download and parse the corpus, as well as qualitative coding approaches to understand the meaning of the content.
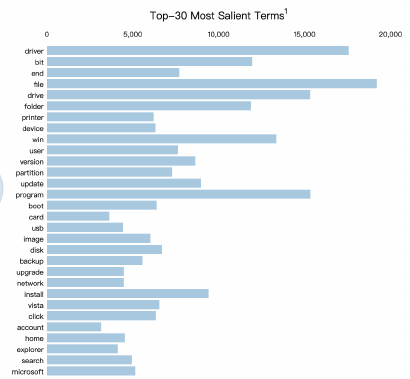
Use LDA and AutoNER to analyze and automatically extract patch issues
Jiaming Lyu
Supervisor: Kami Vaniea
Keeping systems up to date and patched is a challenging job for a system administrator. While installing patches quickly is good for security, not all patches are safe to install as they may break important parts of the system. In this project, I propose a combinative method of using heuristics and Latent Dirichlet Allocation to identify which patches being discussed on a forum are safe to install and which patches have problems.
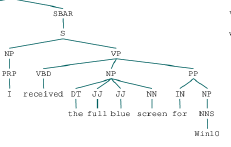
Use forum posts to detect which updates are experiencing problems
Qingyue Zhu
Supervisor: Kami Vaniea
Patching systems quickly can fix system bugs and prevent security issues, however, it may also create new bugs and issues. In this work, I provide patch-issue information at the post level, stentence level, and feature level. My aim is to identify parts of forum posts that discuss patch issues to enable system adminstrators to quicly review only the information important to them and their system. To accomplish this I, used keyword lists to identify posts discussing problems and sentiment analysis to find sentences that express negative sentiment.

Meagle - Crowdsourced software data with community-moderated software reviews
Tom Macmichael
Supervisors: Sebastian Maneth, Kami Vaniea
Finding impartial information about a given piece of software is not easy: there is no single place users can visit to find and contribute information in a consistent manner. This project reated a new website called Meagle, that allows a community of users to review pieces of software with moderation so the best reviews are easy to find.
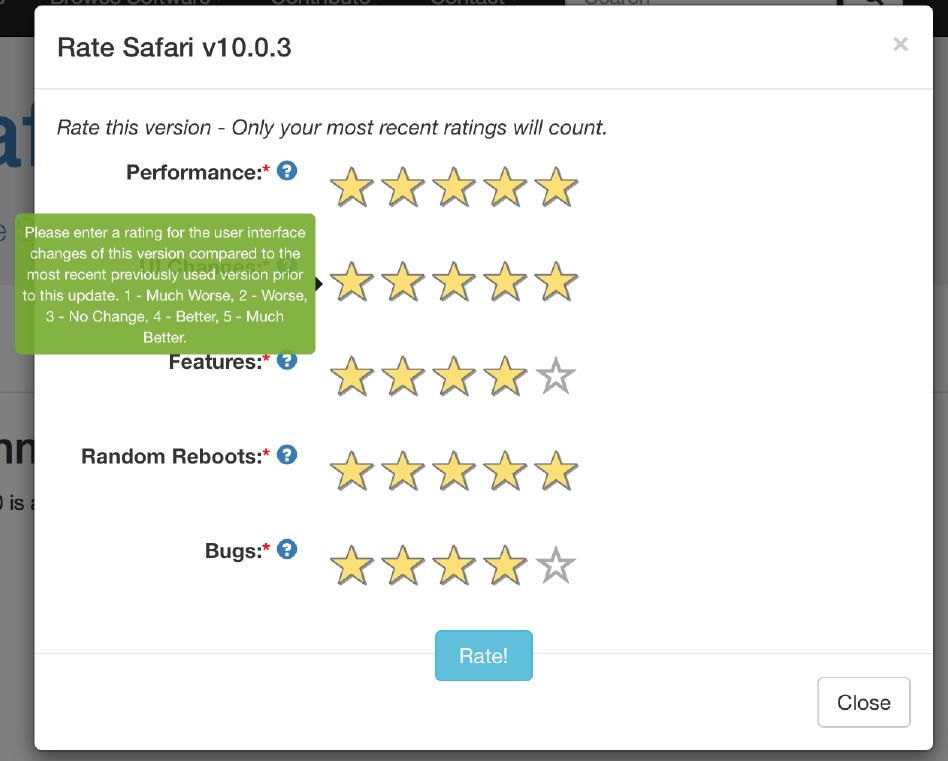
Building a website for users to rate software updates
Kayode Oduyemi
Supervisors: Sebastian Maneth, Kami Vaniea
End users are not particularly aware of the security implications of not installing updates. This project addresses the problem by creating a website where users can comment on and rate software updates.
