PhishEd: Automated Phishing Feedback for End-Users
Phishing is one of the most effective vectors for tricking users into providing sensitive information, such as account details, to attackers who then use the information to harm users, organizations, and society at large. Recent attacks, such as the Colonial Pipeline shutdown in the US can be attributed to phishing. In the UK, 86% of businesses reported receiving phishing attacks1 and while 76% of UK users believe that they can recognize and avoid suspicious links in emails,2 our own research shows that only about 8% can accurately read a URL.3 The staggering £53.7 million lost in the UK in 2020 to impersonation fraud also attests to the problem.4
Employer-provided training tends to be delivered either up-front or given after the employee has fallen for a mock phishing attack. These approaches do work, but they are very employer-centric in that employers choose the time and content of the training. Delivering the same training to everyone also forces a compromise between comprehensively covering topics and containing detailed actionable guidance. For example, training commonly advises users to "look at the destination of links" but does not have the space to explain how to do so. Users in this situation have virtually no agency or control and lack the ability to shape their own learning to match their needs. Users also experience phishing as an infrequent unexpected event that is mixed in with other activities. Phishing by its nature is designed to appear urgent or threatening. A user receiving such a message may be worried or scared about what might happen if they were to ignore it. Currently their only options are to delete the potential phish (scary) or report it and ask for advice (slow).
In this project, we propose a novel phishing-advice tool, PhishEd, which accepts reports from users of potential phishing emails, uses AI to parse out contextual phishing features, and quickly responds back to the user with advice based on the content of the reported email. to explain the reasoning or frame the decision the user needs to make. For example, a reported phishing might contain "HMRC" but have links leading to Dropbox. The auto response would inform the user that the email is not from HMRC (DKIM) and the links lead to Dropbox which HMRC would never use. It would also provide examples from the email to evidence these claims. The objectives of this project are: (i) help users confidently make safety decisions, (ii) teach them skills about how to detect fraud, and (iii) make them want to report phishing in the future.
- NCSC Cyber Security Breaches Survey 2020.
- UK Consumer Digital Index 2019.
- S.S. Albakry, K. Vaniea, M.K. Wolters; What is this URL's Destination? Empirical Evaluation of Users' URL Reading; In Proceedings of the 2020 CHI Conference on Human Factors in Computing Systems. 2020.
- UK Finance, Fraud – The Facts 2021.
Publications
- PhishED: Automated contextual feedback for reporting phishing [bibtex]
A. Jenkins, N. Kokciyan, K. Vaniea; In Proceedings of the Symposium on Usable Privacy and Security Poster Track. 2022. - Context-based Clustering to Mitigate Phishing Attacks [bibtex]
T. Saka, K. Vaniea, N. Kokciyan; In Proceedings of the 15th ACM Workshop on Artificial Intelligence and Security (AISec 2022). 2022. - ``I didn't click'': What users say when reporting phishing [bibtex]
N. Pilavakis, A. Jenkins, N. Kokciyan, K. Vaniea; In Proceedings of the Symposium on Usable Privacy and Security (USEC'23). 2023.
- A Case Study of Phishing Incident Response in an Educational Organization [bibtex]
K. Althobaiti, A. Jenkins, K. Vaniea; In Proceedings of the ACM Conference on Computer Supported Cooperative Work and Social Computing. 2021. - Analysis of publicly available anti-phishing webpages: contradicting information, lack of concrete advice and very narrow attack vector [bibtex]
M. Mossano, K. Vaniea, L. Aldag, R. Düzgün, P. Mayer, M. Volkamer; In Proceedings of the 5th IEEE European Workshop on Usable Security (EuroUSEC). 2020.
People
Current- Adam Jenkins
- Nadin Kokciyan
- Tarini Saka
- Sean Strain
- Jialing Wu
- Kami Vaniea
Funding
Research is funded by REPHRAIN.Related Student Projects
Projects by undergraduates, masters, and intern students that explore topics related to the PhishEd project. Projects are usually inspired by the main project research but each project is the student's own.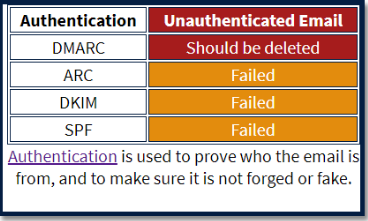
Automatically Generating Contextualised Responses to Phishing Reports
Sean Strain
Supervisors: Kami Vaniea, Adam Jenkins
I propose a novel system that respons to reports of email phishing with contextualised information and advice. The first year of the project analyses a given email for a range of phishing indicators and dynaically generates a set of features that can be used to create a friendly and educational response. The second year of the project involved creating a simulated inbox interface which showed the output of the system in a realistic setting. A study with 22 participants was then used to evaluate how users interacted with the system and how much it helped users identify and learn about phishing.
Correlating Information on Email to Help the User Receive Better Understanding on Identifying Phishing Email
Isa Albashar
Supervisor: Kami Vaniea
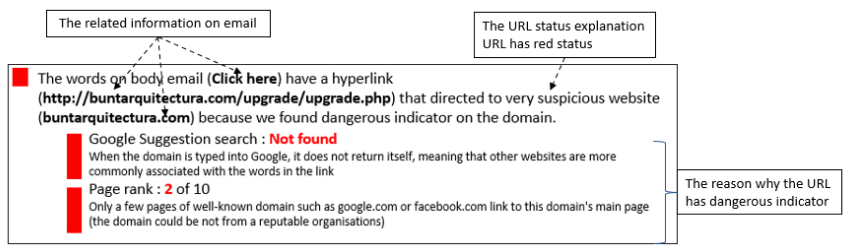
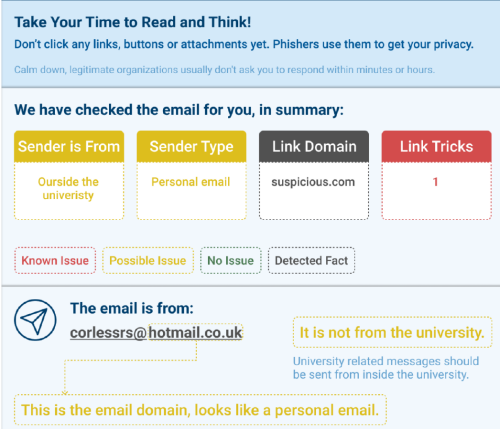
Phishing is a popular method to obtain sensitive data from users such as login passwords. Unfortunately automatic detection methods, while quite accurate, are not 100%, so some phishing emails appear in user inboxes. Users are recommended to report such email, but they are unlikely to get a quick response if they do. In this project I create a prototype for an auto responder system that gives a summary of email analysis which consists of the email features identified and has a friendly explaination.
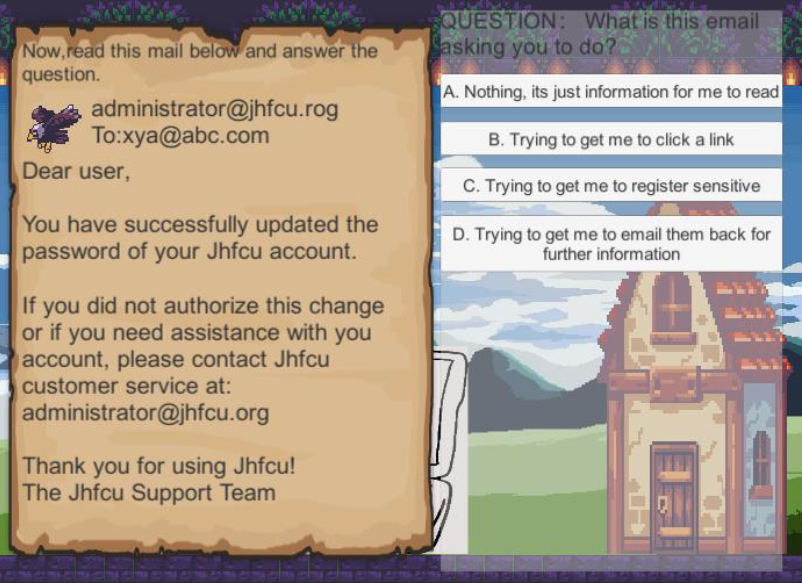
Cyber Security Game: An education game to teach non-technical employees about phishing emails
Wenning Jiang
Supervisor: Kami Vaniea
Phishing emails are one of the most dangerous attacks in recent years, lurking in email inboxes for the unwary. Serious games present a potential way to teach users about phishing in a more fun environment. This project designed a progressive game where the difficultly raises in levels. Thereby increasing the challenge as the player progresses.
Analysis of phishing emails for construction of auto-generated advice
Daria Popova
Supervisor: Kami Vaniea
Phishing is an attack that exploits how people interpret email content, in paricular, exploiting: fear of scarcity, authority, guilt, and gullibility. I perform an analysis of an email dataset using deep neural networks and automated classifiers in an effort to provide users with useful predicted guidance.
The Impact of Cross-National Differences on Phishing Email Detection Ability
Mingyang Dong
Supervisor: Kami Vaniea
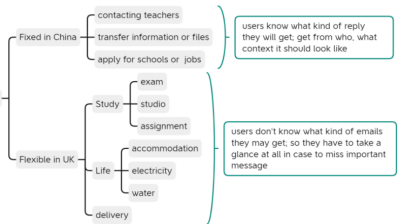
Phishing is a crime that employs both social engineering and technical methods to steal sensitive personal information. People who relocate from a region or culture where communication is done differently can be particularly vulnerable to phishing. One of the most common phishing avoidance advice is to see if the message `looks odd' which is easy for someone who is established in their community or job, but is very challenging for someone who just relocated. This project aims to better understand the phishing-related challenges faced by students who relocated from China to the UK for their studies. We find that University communication in China is normally done over communication channels that verify the sender's identity, like WeChat. Whereas similar communication in the UK is over email which is not properly authenticated. These differences cause challenges for international students.
Designing an Autoresponder for Phishing Email Reports
Zeyu Zhang
Supervisor: Kami Vaniea
Nowadays, it is common for organizations to support their members recognizing phishing by encouraging them to report any suspicious emails. However, as a kind of human assistance, not every inquirer can be responded in minutes, while speed can matter a lot because phishers often press their targets to make immediate decisions by injecting a sense of urgency. In addition, as the help desk workers might not be phishing experts either, their feedback is not always helpful that it might be very general but not customized to a certain reported email. Therefore, I designed an automatic responder for phishing email reports, which is technical feasible to implement to return immediate feedback to the inquirer. According to the design, the responder can automatically parse the reported emails and notify the findings through specific colors and texts, ranging from safe to dangerous. This solution combines the human autonomous decision and more reliable automated detection methods, which cover a wider range of phishing features compared to most user-support tools, including email headers, internal URLs, and email body. Also it focuses on explaining those features to ordinary users. Through user evaluation with 6 non-experts participants, the feedback is demonstrated to be generally comprehensible, helpful and friendly.
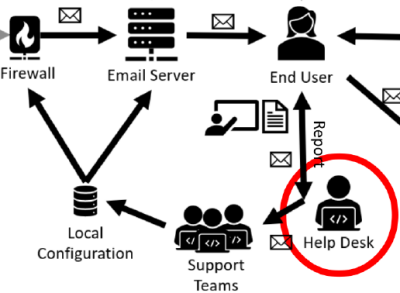
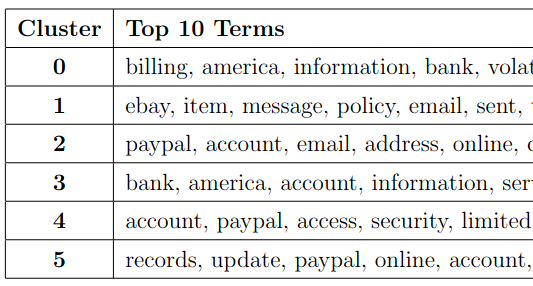
Clustering Phishing Emails to Help the Helpdesk
George Gilligan
Supervisors: Kami Vaniea, Kholoud Althobaiti
In this project I unpack, decode, parse, vectorise and cluster malicious emails, with the intention of grouping them into phishing campaigns. The work is motivated by a desire to automate the work of an organisation helpdesk, who are currently consigned to manual labeling of each phishing email individually. The results show promise that phishing campaings can be clustered.

Web-based tool for estimating security training approaches for security decision-makers
Nan Sheng
Supervisor: Kami Vaniea
Cyber security has been a concern for organizations because it can lead to large financial loss. The premise of this project is that the CISO realizes the improtance of cyber security training and is trying to find a suitable training approach for the staff. This project collects essential information about training approaches from academic papers and training companies such as methodology, charateristic, effectiveness, cost and commercial training products. The goal is to help someone like a CISO select a suitable training approache for the staff.
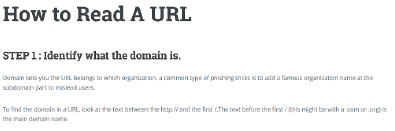
Empirical Evaluation of Users' Ability to Read URLs With and Without a Support Website
Xinding Wang
Supervisor: Kami Vaniea
Reading a URL unaided is challenging. This project had two goals:
1) Determine if people in China and Europe read URLs differently.
2) Build a website that parses and explains a URL to someone in both English and Chinese.
